...Without Making Them So Complex You Don't Remember Them
TIME TO READ: 5 MINUTES
We use passwords every day, protecting important data. But how effective are they?
"Password strength" is how we describe password effectiveness. It's a big issue among cybersecurity professionals…because almost all the passwords we do use are NOT strong.
Here's how to estimate your own passwords' strength, according to the latest data.
Password Strength = How Long it Can Withstand a Cyberattack
The best way to measure password strength is by the amount of time needed to crack it.
Who cracks passwords? Cybercriminals, looking for a way into your network. How do they crack them? By what’s called a brute force attack. Using high-grade video cards and special software to run through thousands of 'guesses' for each password
character.
The longer this takes, the less likely a cybercriminal will put forth the effort. So, one way to keep cybercriminals out of your network, is to make sure everyone uses complex passwords.
How complex? Let's see.
Hive Systems, a cybersecurity solutions provider, recently published a new version of their Password Table. This table illustrates the time it would
take a hacker/cybercriminal to crack a password, depending on two elements: how many characters the password has, and what types of character it uses.
Here's the table:
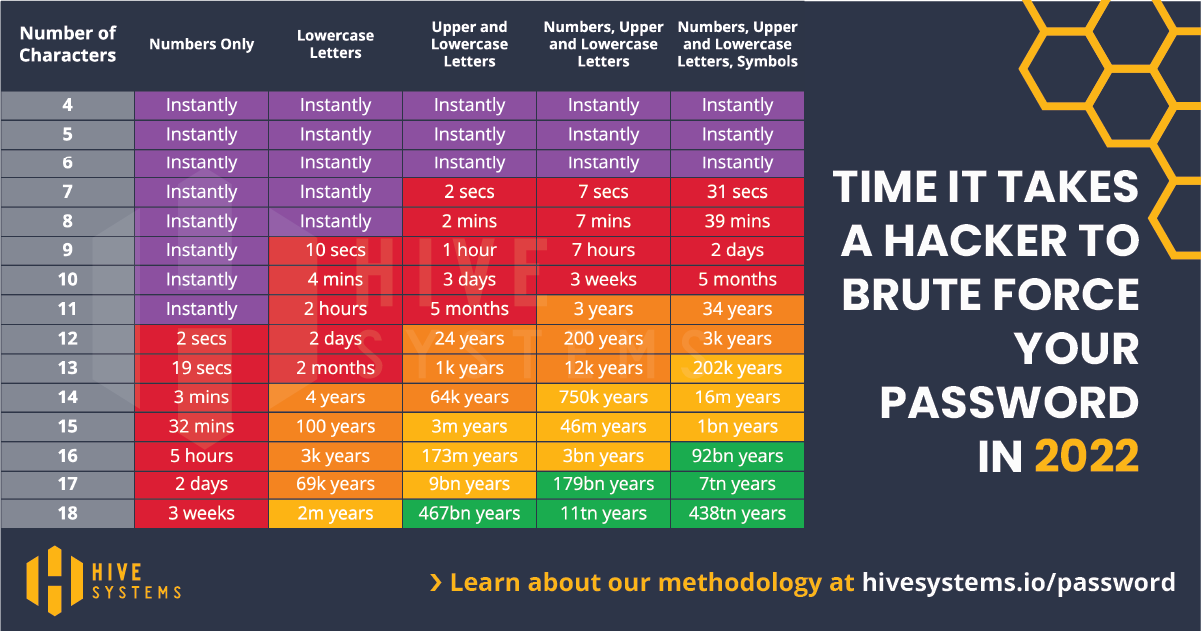
Image courtesy of Hive Systems.
Their post has some incredible data on password security...we encourage you to take a look.
The character types are as follows:
- 1234567 [Numbers]
- lowercase letters
- UPPERCASE LETTERS
- !@#$%^& [Symbols]
The table points out two critical truths:
- No matter how complex a password is, if it's under 9 characters long, a cybercriminal can crack it in minutes or less.
- Even with minimal complexity, long passwords will rebuff cracking attempts for years.
So we have two password factors to consider here. Which is more important, complexity, or number of characters?
According to the table, number of characters. Even weak passwords take longer to crack if they're long. So let's do some length comparisons.
A crossover point in the table comes at 12 characters. That's when you see more orange (improving) cracking times.
How long is 12 characters? This long: 3 words only
Surprisingly short, and pretty easy to remember. It only has two characters types though. Let's add one more: 3 Words Only
According to the table, a cybercriminal would need 200 years to crack this now!
So, if you make passwords long enough to make hacking them "not worth it," you'd need 12 characters at a minimum. Make it a mix of numbers, upper- and lowercase letters.
Here's another example: GoodPass1234%
This is 13 characters long, and incorporates a symbol. The table indicates a crack time of 202,000 years.
Unless you're a top-secret research facility or international bank, no cybercriminal will bother trying to crack passwords that strong. They'll either leave you alone, or try another method to break into your network (like phishing emails).
Want to test your current passwords? Here's a free password tester: Security.org – How Secure is My Password?
How to Remember Strong Passwords Easily
Sticking to passwords 12 characters and longer though…how will you remember them all? With all the online accounts we use these days, this sounds painful.
You don't need to, really. You can make it easier on yourself with two things: A password manager, and a memory heuristic.
Password managers you've heard about before. This is the LastPass / BitWarden / 1Password crowd. But what's a memory heuristic?
This is a convention, a standard which your passwords follow. Think of a group of ideas which all share similar characteristics.
Here are some heuristic examples. You may follow one such heuristic without realizing:
- Animal name + a behavior the animal does NOT do. For example, horses + engineering
- Words + their antonyms. Big/small, wide/narrow, heavy/light, etc.
- Names from world mythologies & legends. Thousands exist!
Add some numbers and 1-2 symbols, and voila! A secure password that will take years to crack.
Now Add MFA for Extra Protection
Multi-Factor Authentication is a security method which combines 2 or more elements to verify your identity. If you've heard the term "Two-Factor Authentication" it's basically the same thing.
MFA examples can include:
- Password + Fingerprint Scanner
- Password + Authenticator App, like Google Authenticator
- Password + Hardware Key
- Password + Code via Text
The combination increases your data security exponentially. It's nigh-impossible for cybercriminals to break in now.
You might wonder, "Isn't this overkill? A strong password can last years. That must be enough." Perhaps. But other factors can make the strongest password vulnerable.
For example, the major business/municipal hacks we see in the news. The most recent one was Okta, a single sign-on service provider.
The breach exposed hundreds of corporate customers' passwords to the world. Within minutes, cybercriminals by the thousands could attack your accounts using passwords exposed in hacks like these.
That's where MFA comes in. They may have your stolen password...but do they have your cell phone? Your fingerprints? No. So they can't get into your computer.
You change the exposed password, and everything's secure once more. MFA saves the day.
It's Easy—and Important—to Make Your Passwords Stronger
You may have heard of efforts to replace the password with other methods – biometrics, blockchain keys, etc. These may one day succeed, and give us something more secure than typing in a password each day.
For now though, passwords rule the authentication world. So let's make them as secure as possible. It only takes a few more taps of the keyboard.
Plan for safe, secure IT in 2022. Take the steps to protect your network. Contact us at sales@planetmagpie.com to review your network's security profile.